IJERPH | Free Full-Text | Development of 222Rn Emanation Sources with Integrated Quasi 2π Active Monitoring
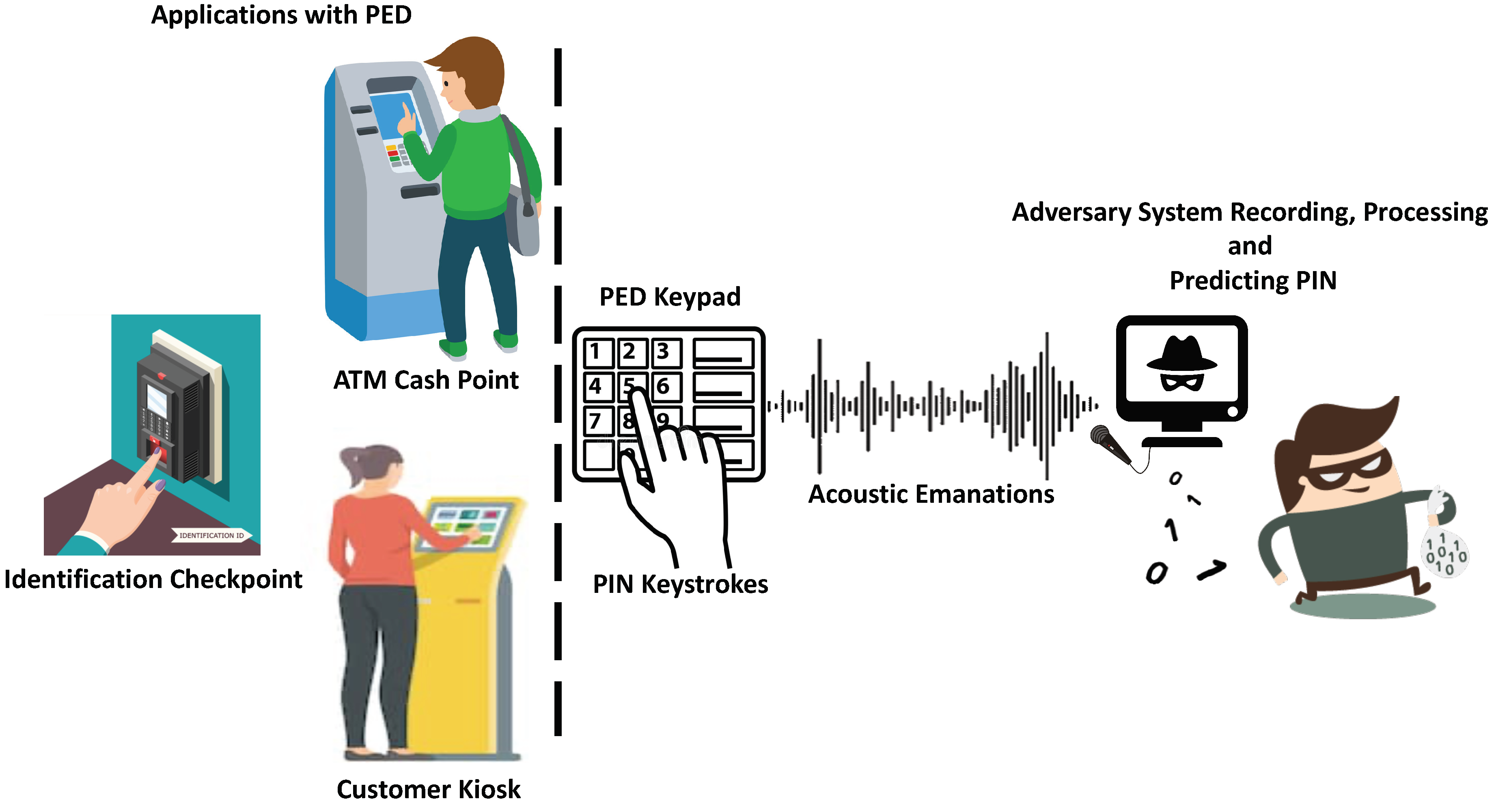
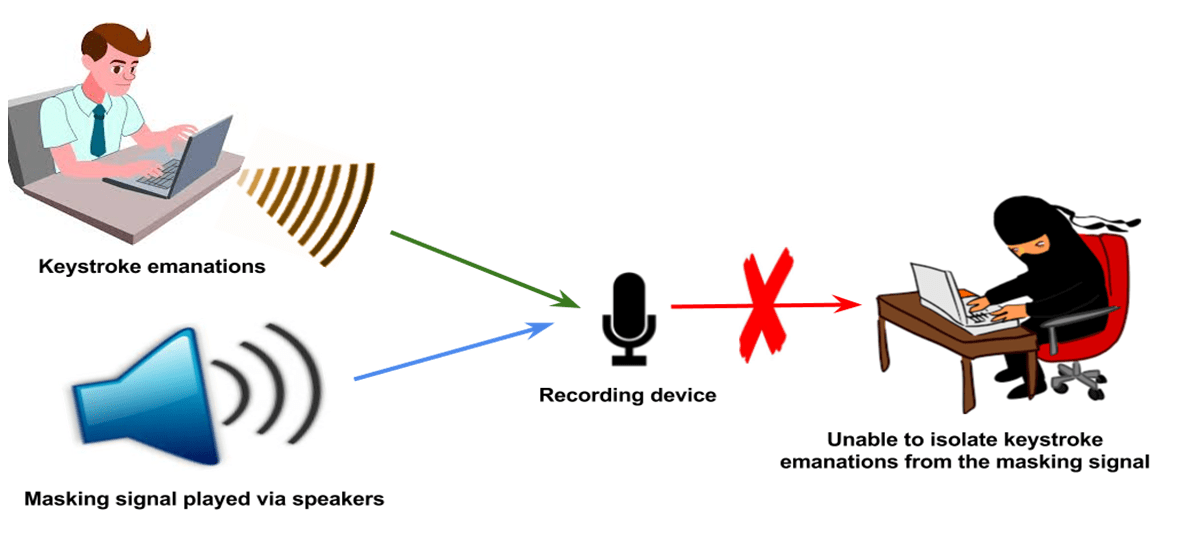
Sensors | Free Full-Text | Behavioral Acoustic Emanations: Attack and Verification of PIN Entry Using Keypress Sounds
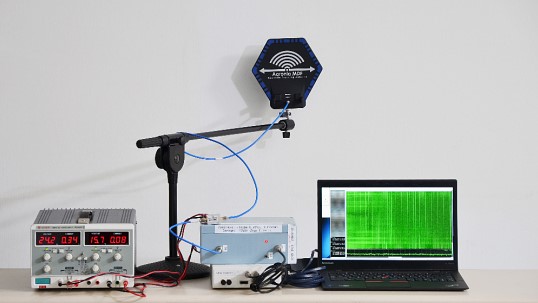
Countermeasures to Prevent Eavesdropping on Unintentional Emanations from Personal Computers | NTT Technical Review
GitHub - evangallagher/NO2-emissions-app: An application that takes NO2 emission data, and feeds a more accurate emanation point using wind data.
Archive Series - Volume 1 - Emanation | Sam Rivers, Cecil McBee, Norman Connors | NoBusiness Records

Sensors | Free Full-Text | Behavioral Acoustic Emanations: Attack and Verification of PIN Entry Using Keypress Sounds

New approaches for analyzing the dynamics of the Rn-222 emanation behavior from Ra-226 sources by means of spectrometric measurement series - PTB.de

Emanation thermal analysis data of vermiculite samples during heating... | Download Scientific Diagram
Countermeasures to Prevent Eavesdropping on Unintentional Emanations from Personal Computers | NTT Technical Review

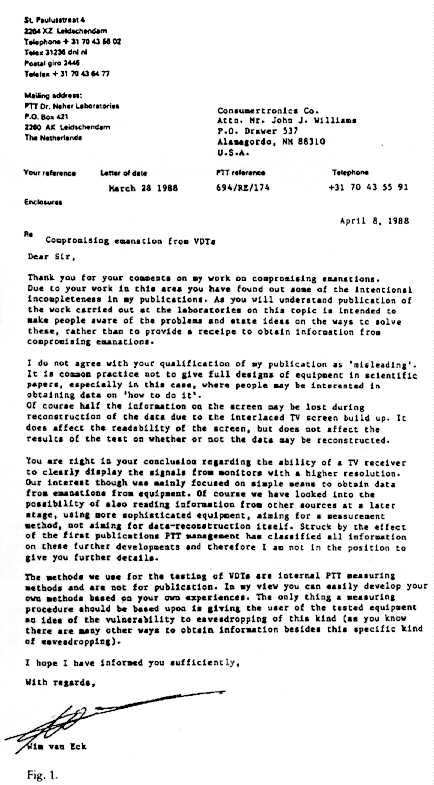
Modeling extreme values resulting from compromising electromagnetic emanations generated by an information system - ScienceDirect